The Dashboard is the default interface used to interact with LumenVox services on a system and being a browser-based application, it has a number of features to help improve the security of connections being made to it. This article describes some of those features and highlights how these may be used. You should review other articles and description of the various configuration parameters in addition to this page, which is intended to give a high-level overview of these security features.
Most of these features can be changed using the Dashboard interface itself to modify the Manager Configuration settings, or by modifying the configuration file on disk directly (manager.conf). whichever method is selected, you should restart the manager process in order to have these changes applied.
Dashboard Security
Often, LumenVox servers are located within large data centers, which have their own security preventing unwanted connectivity between machines, however it is important to understand that there are a number of security features build into the Dashboard that can be enabled as needed. Sometimes these features may be less known, or even overlooked, so this article will try to describe some of these options.
HTTP vs HTTP Connections
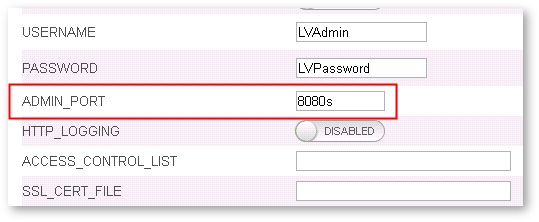
By default, the Dashboard uses HTTPS on port 8080 of the host system, which means that the secure version of HTTP is used. This can be configured to use HTTP instead, however you should understand that by doing so, the connection is not secure.
This setting can be changed using the ADMIN_PORT setting, as shown here:
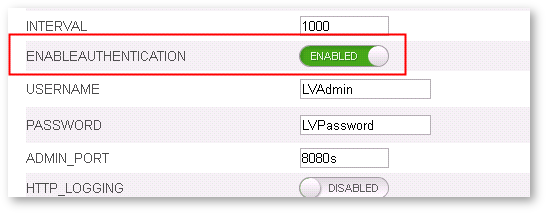
User Authentication
There are also options to specify a username and password that need to be entered before gaining access to the Dashboard. These are the USERNAME and PASSWORD options as shown below. It is recommended to enable the HTTPS protocol described above when using User Authentication to prevent the username and password from being sent using plain text, which is clearly not secure at all.

Note that in order to enable the use of USERNAME and PASSWORD settings, you must also enable the ENABLEAUTHENTICATION setting, as shown here:
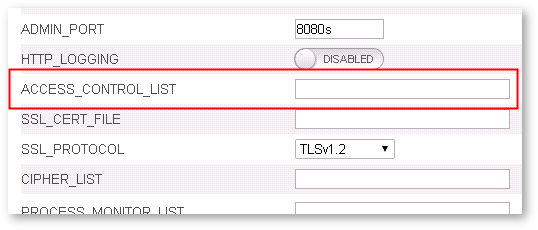
Access Control List
An additional security option allows you to restrict the IP address range of computers that are able to access the dashboard. This may be useful if you would like to restrict access to only a small number of machines, or perhaps a subnet, thereby preventing any machines from an unknown network from accessing the dashboard.
To enable this feature, use the ACCESS_CONTROL_LIST option, which allows you to specify an optional Access Control List (ACL). This is a comma separated list of IP addresses to allow or deny access to.
SSL Certificate File
The HTTPS protocol uses a specially signed Server Certificate as part of the secure negotiation when a browser opens a page on a website. This certificate mechanism is used to validate that the machine you are connecting to is really the machine you think it is, and not some impostor.
These certificates are generally obtained though various trusted online Certificate Authority organizations, who perform this validation before issuing certificates - the overall details of this mechanism are beyond the scope of this article, but there are many references online.
By default, there is a Self-Signed Certificate, which was generated by LumenVox and included within the installation package - this is not a valid (signed) certificate for your machine, but merely a placeholder for a correctly-signed certificate, which is typically obtained on a per-server basis.
Users are often confused by the error message that comes up when first opening the dashboard page, which reports an invalid certificate - this is correct, since you need to obtain your own certificate for that machine and it can be installed somewhere, then referenced using the SSL_CERT_FILE configuration option, which resolves the issue, as shown here:
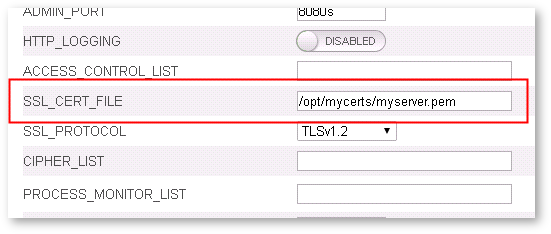
The secure connection works perfectly fine, and is completely secure, when using this default (self-signed) certificate, however if you wish to verify the identity of the machine you're connecting to, you should obtain a valid signed certificate. We have an article named Resolving Dashboard Certificate Issues that describes this process in more detail.
SSL Protocol and Cipher List
Advanced users may wish to control the SSL parameters governing which Transport Layer Security (TLS) protocol is used for connections to the dashboard. This can be controlled using the SSL_PROTOCOL option, highlighted here:
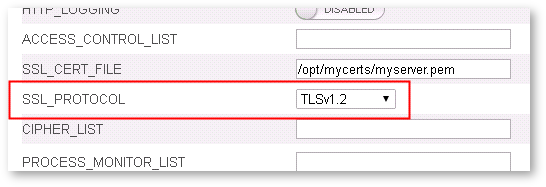
By default, the TLSv1.2 protocol is used, and is the most secure, so we recommend selecting this unless you have a very good reason to use one of the other settings. Note that TLSv1.0 has been deemed insecure, and is only available here for backward compatibility with older browsers if the newer protocol cannot be used.
An additional advanced setting allows users to specify which Cipher List should be used when negotiating the secure HTTPS connection - this is the CIPHER_LIST setting. If nothing is specified for this (the default) then the Cipher List built into the openssl library will be used, allowing the browser to negotiate one of those specified. This setting should only be changed by users understanding the implications of making this change.

Other Security Considerations
There are some other security considerations when reviewing the overall security of a system. We have a knowledge base article named Securing Sensitive Data, which contains some helpful information along with a link to our recommendations document.